By default, Insights On-Premises (IOP) creates its own self-signed certificate once you deploy a new IOP appliance. When connecting to the IOP server from the browser, a warning message indicates that the certificate is not valid for the site.
Instead of using the self-signed certificate, we recommend using a certificate from a trusted certificate authority (CA). In this article, we show you how to replace the self-signed certificate with a certificate trusted by a certificate authority. There are several ways to perform this task. Our recommended steps are outlined below.
How to Replace a Certificate
-
SSH into the IOP server. Log in with the user cuadmin and use the password you created during the OVA deployment.
ImportantDue to security reasons, the root user is deactivated by default from version 8.6 and higher.
-
Run hostname to get the fully-qualified domain name (FQDN) of the IOP machine.
cuadmin@iopserver [ ~ ]$ hostname iopserver.AD2012.LOC -
In your DNS configuration, create an A Record and make sure the hostname resolves.
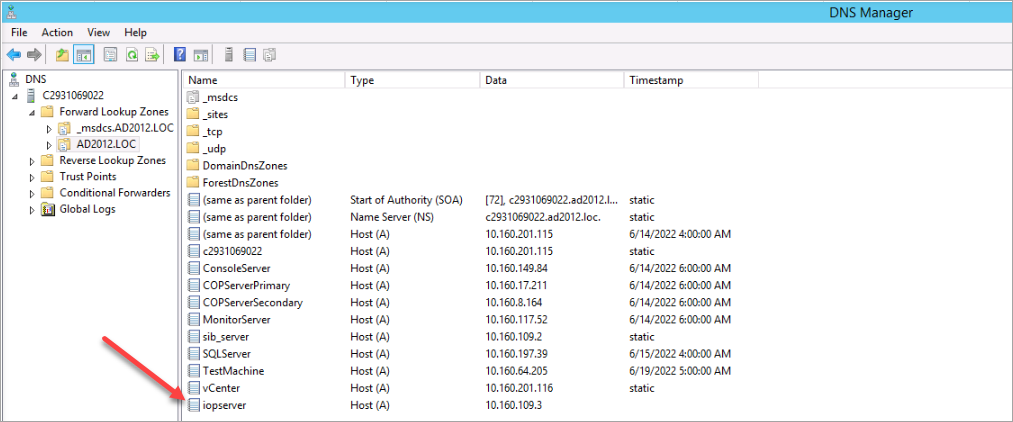
Ping the hostname of the IOP server to verify that it can be resolved. The ICMP protocol is deactivated on the IOP server. The DNS configuration is correct if the IP address of the IOP machine is correctly displayed.
-
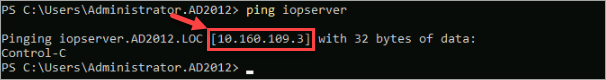
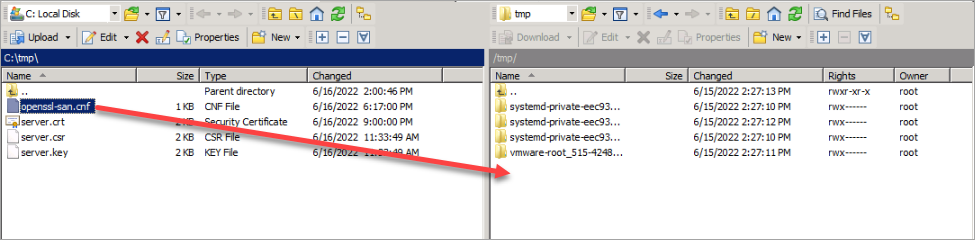
Download the attached file openssl-san.cnf and replace the hostname and the DNS entries in the red-marked fields.
-
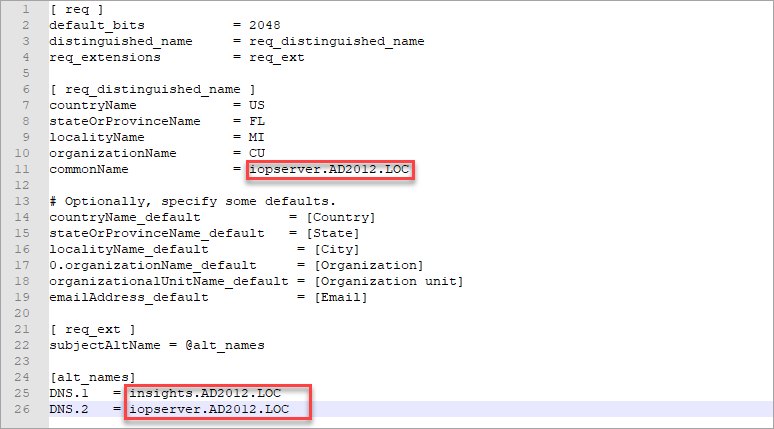
Once done, copy the file to the /tmp folder of your IOP server using WinSCP or any other file transfer tool.
-
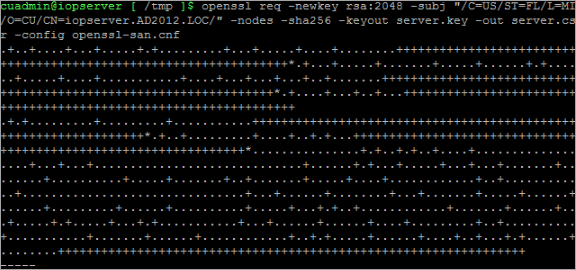
Once you uploaded the file to the /tmp folder, run the following commands on the IOP machine:
cuadmin@iopserver [ ~ ]$ cd /tmp openssl req -newkey rsa:2048 -subj "/C=US/ST=FL/L=MI/O=CU/CN=iopserver.AD2012.LOC/" -nodes -sha256 -keyout server.key -out server.csr -config openssl-san.cnfChange the -subj param values to match what you entered on .cnf file. Make sure to use server as the name for the csr and key file.
-
The private key is generated when you see the following message:
-
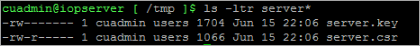
Verify that both files, server.key and server.csr, have been created.
-
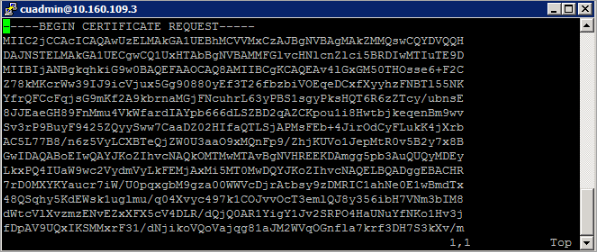
Submit the server.csr to your Certificate Authority. Create a certificate from your Enterprise CA or preferred public CA and make sure that you use a Web Server certificate, using the same template. Make sure to download the cert in Base64 Encoded.
In our case, we use AD CS Web Enrollment to create the web server certificate.
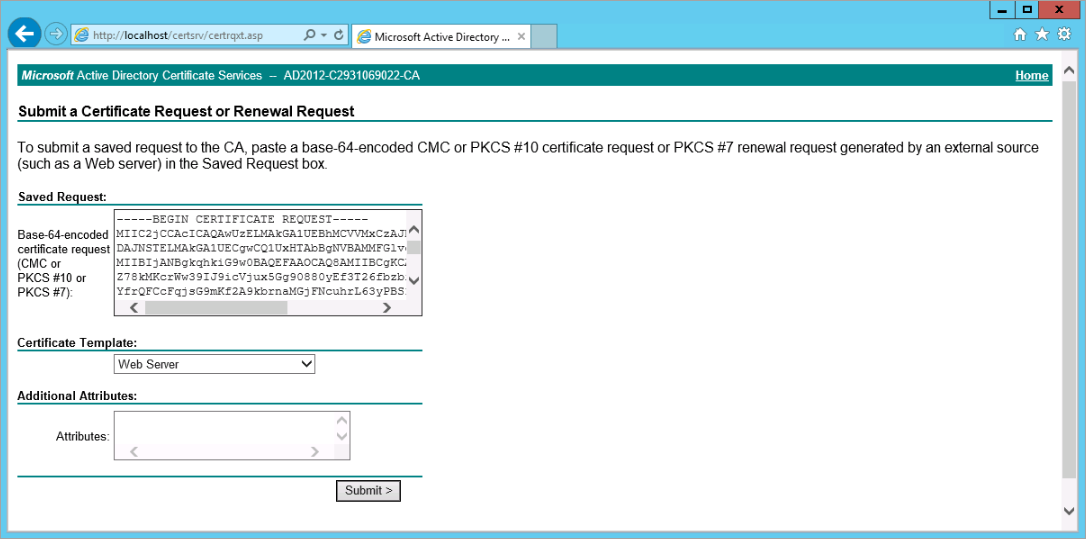
Copy the certificate request, submit and create the certificate.
Make sure you download the certificate in Base 64 encoding

- On the IOP server, back up the original files certificate files in
/opt/iop_volumes/config/iop_proxy/ssl. Use the following command to back up the certificate and private key file:
sudo mv server.crt server.crt.bak
sudo mv server.key server.key.bak
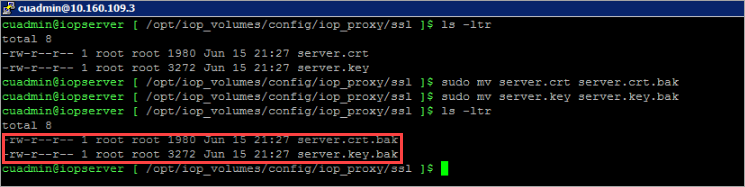
-
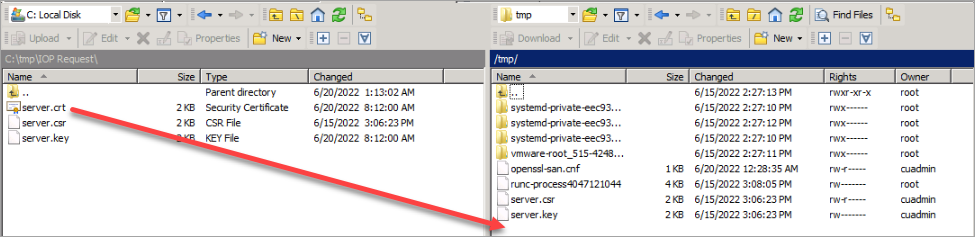
On the machine where you stored the certificate file, rename the certificate file to server.crt and copy the server.crt and the server.key to the
/tmpdirectory on the IOP server.
-
Move the server.crt and server.key files to the
/opt/iop_volumes/config/iop_proxy/sslfolder.cd /tmp sudo mv server.crt /opt/iop_volumes/config/iop_proxy/ssl sudo mv server.key /opt/iop_volumes/config/iop_proxy/ssl -
Run the following command
sudo docker container exec iop_proxy nginx -s reload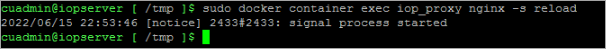
-
Check if the certificate is valid by logging in to Insights again using HTTPS.
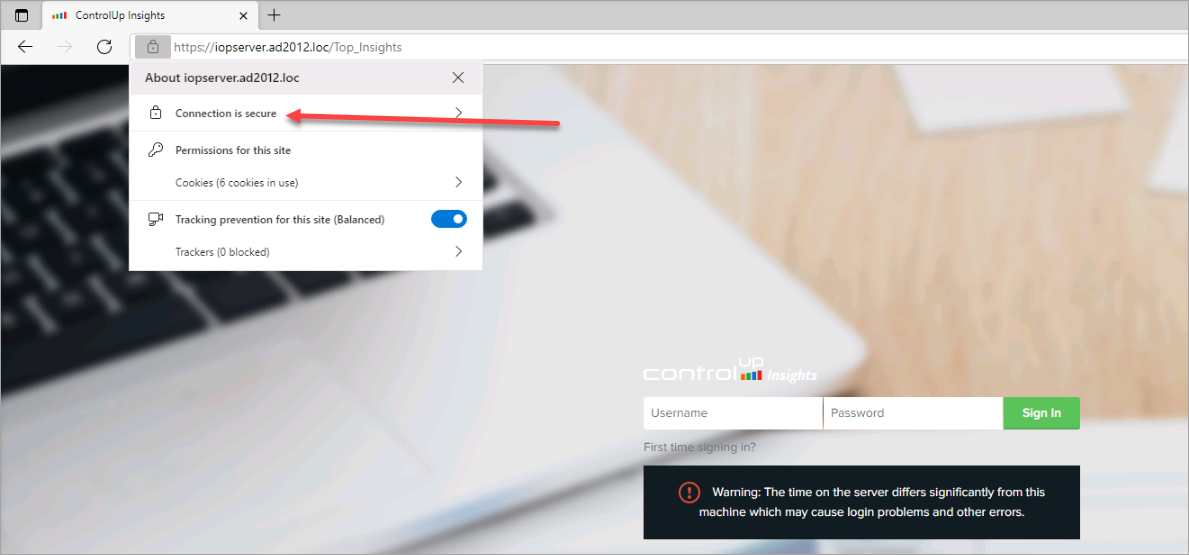
In this article, you learned, how to replace the self-signed certificate with a certificate trusted by a certificate authority.